About
The XML Bomb scan checks if your service has efficient protection against an XML bomb.
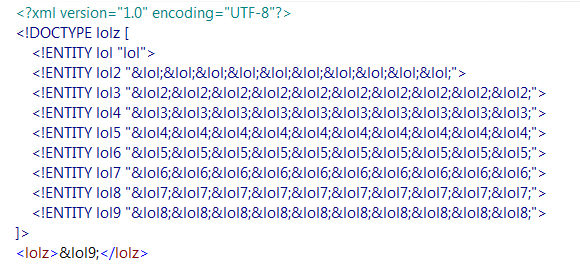
Typically, attackers try to use an XML bomb to cause service response delays and general instability leading to the denial of the service. The XML bomb scan creates such a bomb for you to ensure attacks of that type would not cause significant harm. For example, the following XML snippet will deny the service of a vulnerable server and possibly cause a crash:
The triggering entity, which in this case is &lol9;, is usually inserted into a parameter of a request.
If the scan does not reveal any information about possible vulnerabilities, it passes successfully.
If the scan has Failed, that may indicate your service is vulnerable to unexpected value types and exposes sensitive information.
Requirements
This scan is applicable to SOAP test steps or requests that contain XML data.
How it works
The XML Bomb scan includes an XML bomb in the request – either inside the message, or as an attachment.
| Note: | Unprotected servers may become unreachable or crash after this attack. |
This scan uses assertions to validate each response and check if it includes any information about potential vulnerabilities.
If a response passes all assertions, PASS will be logged for that response. If any assertion fails, FAIL will be logged.
 |
If you have not applied any assertions to the scan, Unknown will be logged for the response. |
Assertions
-
Default Assertion
Sensitive Information Exposure – Verifies that your server does not reveal any information that is useful for attacks (such as stack traces, if the server crashes). -
Recommended Assertion
Response SLA – Verifies that your service responds within expected time even after receiving unexpected input.
Parameters
The XML Bomb scan works by inserting values into the message parameters.
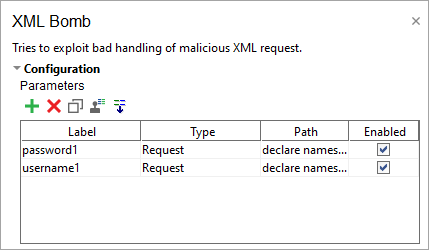
Normally, parameters are extracted automatically when you create the scan. See Parameters for more information.
Use the following options to configure the scan Strategy:
| Option | Description |
|---|---|
| Select Strategy | One by One – Select to use requests one by one (may take some time). All At Once – Select to use all requests at once. |
| Request Delay (ms) | Set a pause between requests during the scan in milliseconds. |
| Apply to Failed Test Steps | Select to run the scan even if the target test step fails. |
| Run only once | Select to run the scan only once for each test step, even if ReadyAPI runs that step several times for a test case. |
On the Advanced panel, define values to be inserted into parameters.
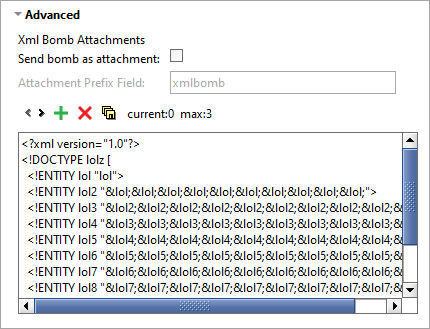
| Option | Description |
|---|---|
| Send as attachment | Send the XML bomb as an attachment instead of a message. |
| Attachment prefix field | Use this prefix when sending an attachment. |
Use the Advanced panel toolbar controls to work with the XML bombs for the scan:
| Option | Description |
|---|---|
| Move to the previous XML bomb. | |
| Move to the next XML bomb. | |
| Create a new XML bomb. | |
| Delete an XML bomb. | |
| Save an XML bomb to a file. | |
 |
The currently selected XML bomb. |
 |
The number of XML bombs. |
Related materials
See Also
Malformed XML Scan
Sensitive Information Exposure Assertion
Response SLA Assertion
Security Scans Types