About
The Fuzzing scan checks how your service behaves when getting random input.
Typically, an attacker tries to throw random values to cause unexpected behavior at web service operations, so the service reveals the system data through error messages or stack traces. The Fuzzing scan checks how your service acts in such cases by sending totally random input data repeatedly for a prolonged period of time.
If the scan does not reveal any information about possible vulnerabilities, it passes successfully.
If the scan has Failed, that may mean there are instabilities in your service, or iterative requests cause security problems or reveal sensitive data.
Requirements
This scan is applicable to all types of test steps or requests.
| Note: | When you use this scan with POST requests containing the JSON data, it does not operates with JSON fields. To check whether your service handles the random JSON input properly, use the JSON Fuzzing Scan instead. |
How it works
The Fuzzing scan generates totally random input for the specified request parameters for a certain number of requests to provoke some kind of unexpected behavior.
It uses assertions to validate each response and check if it includes any information about potential vulnerabilities.
If a response passes all assertions, PASS will be logged for that response. If any assertion fails, FAIL will be logged.
 |
If you have not applied any assertions to the scan, Unknown will be logged for the response. |
Assertions
-
Default assertion
Sensitive Information Exposure – Verifies that your server does not reveal any information that is useful for attacks (such as stack traces if the server crashes). -
Recommended Assertion
Valid HTTP Status Codes – Verifies that the request does not return the server error HTTP status code.
Parameters
The Fuzzing scan inserts values into the message parameters.
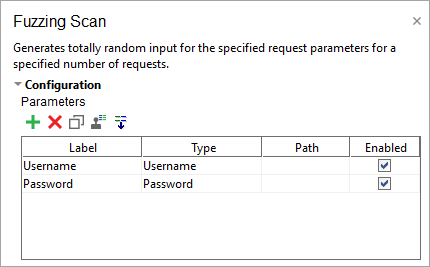
Normally, parameters are extracted automatically when you create the scan. If there are no parameters present, ReadyAPI will not run the Fuzzing scan. See Parameters for more information.
Use the following options to configure the scan Strategy:
| Option | Description |
|---|---|
| Select Strategy | One by One – Select to use fuzzing requests one by one (may take some time). All At Once – Select to use all fuzzing requests at once. |
| Request Delay (ms) | Set a pause between requests during the scan in milliseconds. |
| Apply to Failed Test Steps | Select to run the scan even if the target test step fails. |
| Run only once | Select to run the scan only once for each test step, even if ReadyAPI runs that step several times for the test case. |
The Advanced parameters define behavior and limits for the scan:
| Option | Description |
|---|---|
| Min length | The minimum length of the fuzzed parameter. |
| Max length | The minimum length of the fuzzed parameter. |
| Number of Requests | The number of fuzzed requests to send. |
Related materials
See Also
HTTP Method Fuzzing Scan
JSON Fuzzing Scan
Sensitive Information Exposure Assertion
Valid HTTP Status Codes Assertion
Security Scans Types
