About
The Boundary scan checks if your service handles unexpected input values correctly.
Typically, attackers try to send values that fall outside of the expected range, causing the service to reveal the system data through error messages or stack traces. The Boundary scan checks how your service acts in such cases by sending various unexpected inputs. For example, for an input field that accepts any integer value between 1 and 10, the Boundary scan checks its behavior if a user enters 20 or -5. Being the data-driven test executed in a loop, it replaces existing values with new ones.
If the scan does not reveal any information about possible vulnerabilities, it passes successfully.
If the scan has Failed, that may mean your service is sensitive to values that fall outside of the normal range, and its vulnerabilities are exposed.
Requirements
The Boundary scan has the following requirements:
-
It only works with SOAP APIs.
-
API definition must include restrictions.
If your API does not fit the requirements, the scan is skipped.
How it works
The Boundary scan replaces the original parameters of a test step or request with values violating the boundaries defined in the web service definition.
Currently, the Boundary scan identifies and processes the following boundaries:
xsd:minxsd:maxxsd:lengthxsd:minInclusivexsd:maxInclusivexsd:minExclusivexsd:maxExclusivexsd:totalDigitsxsd:fractionDigits
| Note: | The unconstrained parameters will keep their original values. |
The Boundary scan uses assertions to validate each response and check if it includes any information about potential vulnerabilities.
If a response passes all assertions, PASS will be logged for that response. If any assertion fails, FAIL will be logged.
 |
If you have not applied any assertions to the scan, Unknown will be logged for the response. |
Assertions
-
Default assertion
Sensitive Information Exposure – Validates that your server does not reveal any information that is useful for attacks (such as stack traces if the server crashes). -
Recommended assertion
Response SLA – Validates that your service responds within expected time even after receiving unexpected input.
Parameters
The Boundary scan works by inserting values into the message parameters.
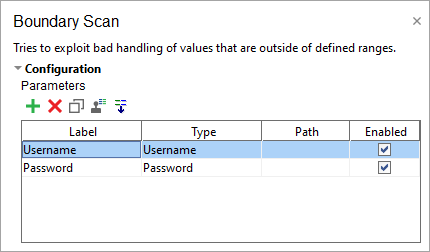
Normally, parameters are extracted automatically when you create the scan. If there are no parameters present, ReadyAPI will not run the Boundary scan. See the Parameters section for more information.
Use the following options to configure the scan Strategy:
| Option | Description |
|---|---|
| Select Strategy | One by One – Select to check boundaries one by one (may take some time). All At Once – Select to check all boundaries at once. |
| Request Delay (ms) | Set a pause between requests during the scan in milliseconds. |
| Apply to Failed Test Steps | Select to run the scan even if the target test step fails. |
| Run only once | Select to run the scan only once for each test step, even if ReadyAPI runs that step several times for a test case. |
